VeraCrypt 1.24 發布,VeraCrypt 是 TrueCrypt 的分支,於2013年6月發布,項目的主要開發者是來自法國的安全顧問 Mounir Idrassi 。Idrassi 創建 VeraCrypt 分支的動機是在 2012 年他被要求在客戶產品中整合 TrueCrypt,他評估了 TrueCrypt代碼后發現它存在一些問題,TrueCrypt 的主要弱點是不能防禦暴力破解攻擊。在加密系統分區時,TrueCrypt 使用 PBKDF2-RIPEMD160 演算法進行 1000 次迭代;對於標準容器和非系統分區,TrueCrypt 最多迭代 2000 次。相比之下,VeraCrypt 使用 PBKDF2-RIPEMD160 演算法對系統分區迭代 327,661 次,對於標準容器和非系統分區,迭代次數進一步增加到 655,331 次,大幅增加暴力破解難度。結果是,VeraCrypt 打開加密分區的速度略慢,而它的加密格式也不兼容於 TrueCrypt。另一個 TrueCrypt 分支 CipherShed 項目則努力兼容 TrueCrypt 加密格式。(以上介紹內容來自 Solidot)
VeraCrypt 增強了用於系統和分區加密的演算法的安全性,使其免受暴力破解攻擊。VeraCrypt 還解決了TrueCryp t中發現的許多漏洞和安全問題。 以下帖子描述了一些改進和更正:https://veracrypt.codeplex.com/discussions/569777#PostContent_1313325
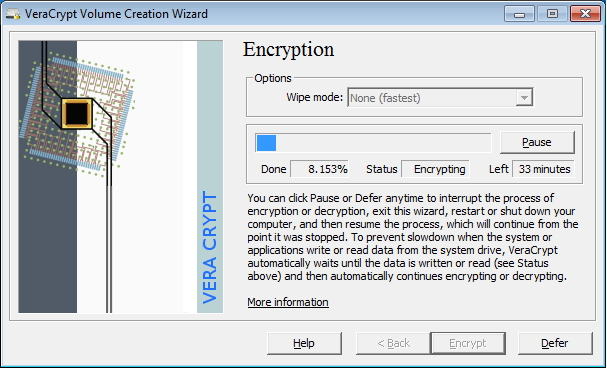
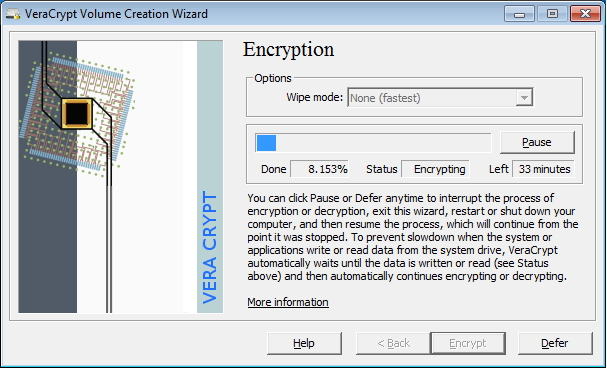
VeraCrypt on the fly encrypting the system partition :
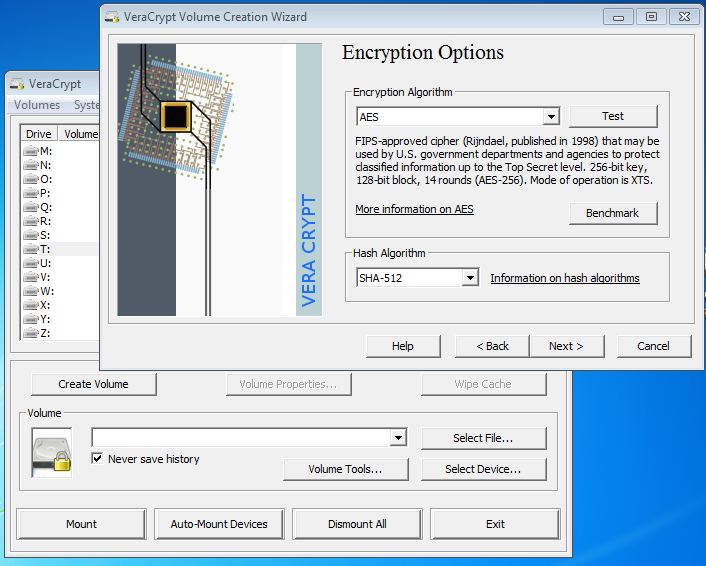
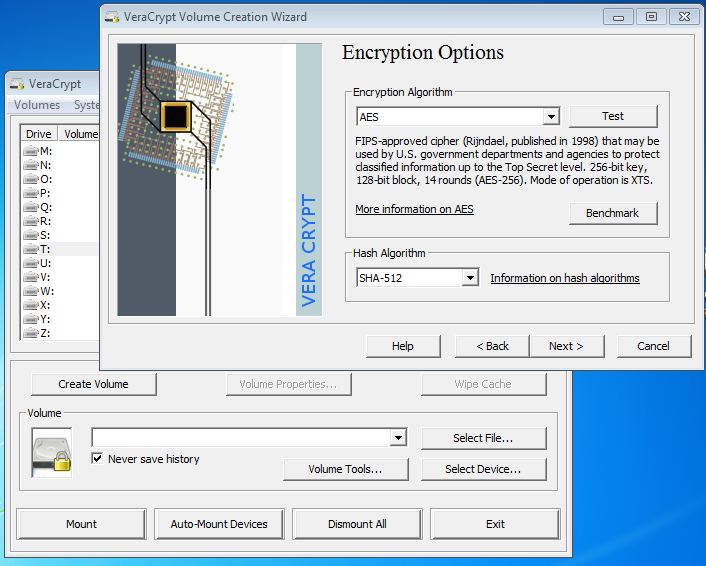
VeraCrypt creating an encrypted volume :
完整改進記錄包括:
-
All OSs:
- Increase password maximum length to 128 bytes in UTF-8 encoding for non-system volumes.
- Add option to use legacy maximum password length (64) instead of new one for compatibility reasons.
- Use Hardware RNG based on CPU timing jitter "Jitterentropy" by Stephan Mueller as a good alternative to CPU RDRAND (http://www.chronox.de/jent.html)
- Speed optimization of XTS mode on 64-bit machine using SSE2 (up to 10% faster).
- Fix detection of CPU features AVX2/BMI2. Add detection of RDRAND/RDSEED CPU features. Detect Hygon CPU as AMD one.
-
Windows:
- Implement RAM encryption for keys and passwords using ChaCha12 cipher, t1ha non-cryptographic fast hash and ChaCha20 based CSPRNG.
- Available only on 64-bit machines.
- Disabled by default. Can be enabled using option in UI.
- Less than 10% overhead on modern CPUs.
- Side effect: Windows Hibernate is not possible if VeraCrypt System Encryption is also being used.
- Mitigate some memory attacks by making VeraCrypt applications memory inaccessible to non-admin users (based on KeePassXC implementation)
- New security features:
- Erase system encryption keys from memory during shutdown/reboot to help mitigate some cold boot attacks
- Add option when system encryption is used to erase all encryption keys from memory when a new device is connected to the system.
- Add new driver entry point that can be called by applications to erase encryption keys from memory in case of emergency.
- MBR Bootloader: dynamically determine boot loader memory segment instead of hardcoded values (proposed by neos6464)
- MBR Bootloader: workaround for issue affecting creation of hidden OS on some SSD drives.
- Fix issue related to Windows Update breaking VeraCrypt UEFI bootloader.
- Several enhancements and fixes for EFI bootloader:
- Implement timeout mechanism for password input. Set default timeout value to 3 minutes and default timeout action to "shutdown".
- Implement new actions "shutdown" and "reboot" for EFI DcsProp config file.
- Enhance Rescue Disk implementation of restoring VeraCrypt loader.
- Fix ESC on password prompt during Pre-Test not starting Windows.
- Add menu entry in Rescue Disk that enables starting original Windows loader.
- Fix issue that was preventing Streebog hash from being selected manually during Pre-Boot authentication.
- If "VeraCrypt" folder is missing from Rescue Disk, it will boot PC directly from bootloader stored on hard drive
- This makes it easy to create a bootable disk for VeraCrypt from Rescue Disk just by removing/renaming its "VeraCrypt" folder.
- Add option (disabled by default) to use CPU RDRAND or RDSEED as an additional entropy source for our random generator when available.
- Add mount option (both UI and command line) that allows mounting a volume without attaching it to the specified drive letter.
- Update libzip to version 1.5.2
- Do not create uninstall shortcut in startmenu when installing VeraCrypt. (by Sven Strickroth)
- Enable selection of Quick Format for file containers creation. Separate Quick Format and Dynamic Volume options in the wizard UI.
- Fix editor of EFI system encryption configuration file not accepting ENTER key to add new lines.
- Avoid simultaneous calls of favorites mounting, for example if corresponding hotkey is pressed multiple times.
- Ensure that only one thread at a time can create a secure desktop.
- Resize some dialogs in Format and Mount Options to fix some text truncation issues with non-English languages.
- Fix high CPU usage when using favorites and add switch to disable periodic check on devices to reduce CPU load.
- Minor UI changes.
- Updates and corrections to translations and documentation.
-
MacOSX:
- Add check on size of file container during creation to ensure it's smaller than available free disk space. Add CLI switch --no-size-check to disable this check.
-
Linux:
- Make CLI switch --import-token-keyfiles compatible with Non-Interactive mode.
- Add check on size of file container during creation to ensure it's smaller than available free disk space. Add CLI switch --no-size-check to disable this check.